TL;DR: Cloudflare blocks vanilla Selenium by fingerprinting the browser, inspecting headers, and analyzing behavioral signals. This guide walks through five practical bypass methods (Undetected ChromeDriver, Selenium Stealth, SeleniumBase UC mode, CAPTCHA-solver integration, and scraping APIs), complete with Python code, a comparison table, and a troubleshooting runbook so you can pick the right approach for your scale and budget.
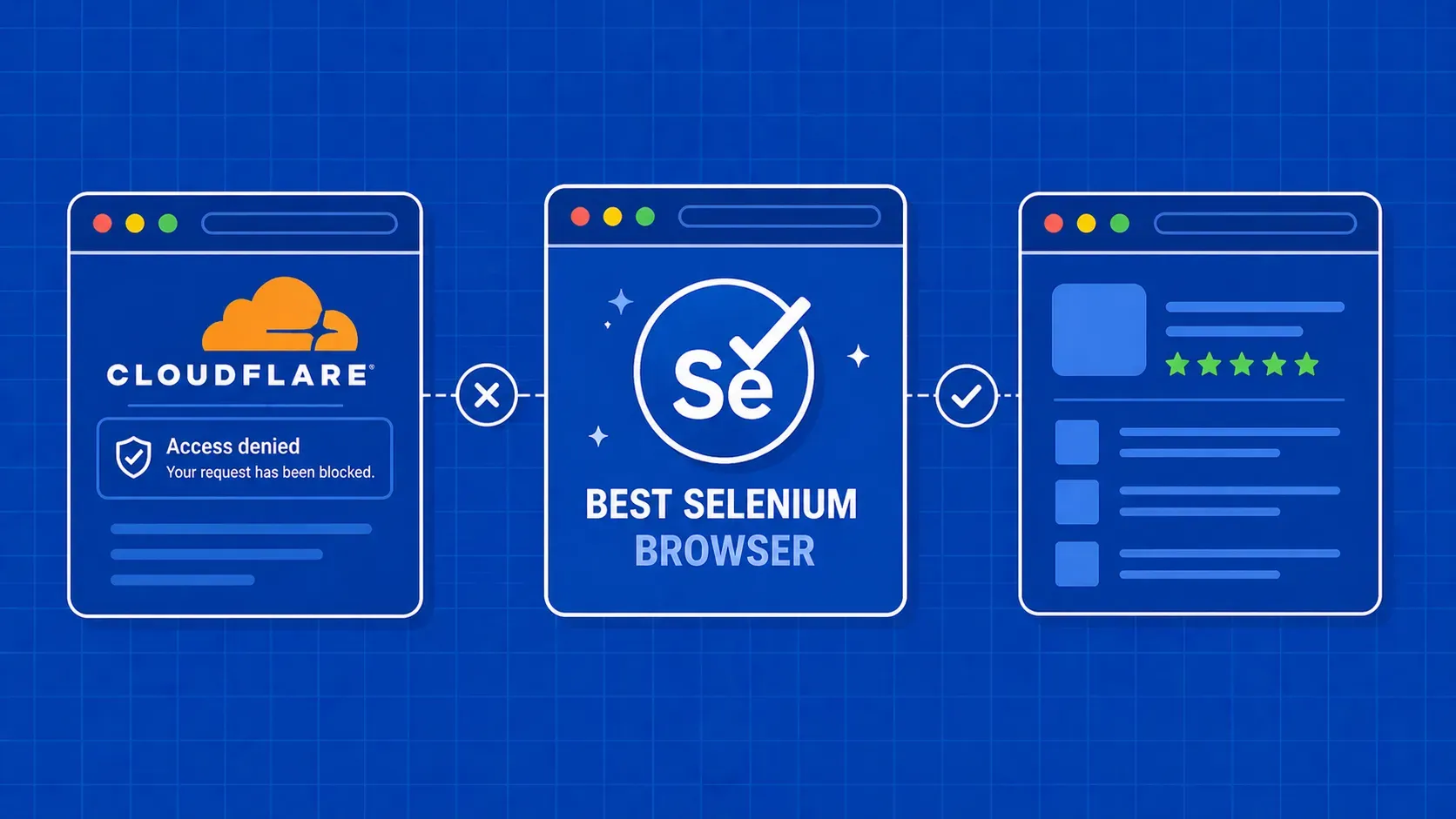
If you've tried to scrape or automate a Cloudflare-protected site with Selenium, you've probably hit the "Checking your browser" interstitial, a 403 wall, or an infinite challenge loop. Cloudflare is a content delivery network and security layer that sits between the origin server and every visitor, actively filtering automated traffic. To bypass Cloudflare with Selenium you need to understand what Cloudflare inspects, then pick a tool or technique that addresses those detection vectors.
In this guide we break down the main ways Cloudflare spots bots, then walk through five distinct bypass strategies in Python, each with working code. We also include a method comparison table, cross-cutting hardening tips (proxies, headers, browser profiles), and a troubleshooting section for the most common failure modes. Whether you're running a handful of QA checks or scraping thousands of pages, you'll find a method here that fits your situation and budget.